- Solutions
- Technology
- Customers
-
Resources
- Resources
-
-
-INPI-AIWEBINAR-Webinar%20(3).png?length=1000&name=(LI-Banner)-INPI-AIWEBINAR-Webinar%20(3).png)
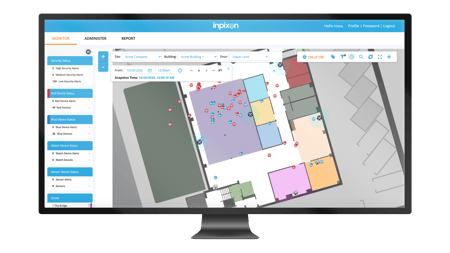
Improve Production Processes with Gen-AI & RTLS
Watch Today > -
RTLS Playbook For Advanced Manufacturing & Intralogistics
Download White Paper > -

Location Intelligence for Safety and Profitability in Mining Operations
Watch Today >
-
- Company


 The Importance of
The Importance of 
